Use a VPN on Your Work Computer: The Dos, Don’ts, and Why It Matters
Use a vpn on your work computer the dos donts and why it matters to stay productive, secure, and compliant. Quick fact: a VPN can protect sensitive data and help you stay private even when you’re on public Wi‑Fi. Below is a practical, step‑by‑step guide with real‑world tips, examples, and the latest data you need to know.
- For broader context, consider this: nearly 85% of remote workers say they use at least one VPN regularly to access corporate resources, while 70% of IT teams report increased demand for VPN solutions post‑2020. These numbers show VPNs aren’t a “nice-to-have” anymore—they’re a must for many workplaces.
Introduction: quick guide to the dos, don’ts, and why it matters What you’ll get in this guide:
- A straightforward set of best practices the dos to keep data safe without slowing you down.
- Clear don’ts to avoid common security missteps that could cost you or your company.
- The why: what VPNs actually defend, where they shine, and where they have limits.
- Practical workflows you can adopt today, plus troubleshooting tips.
- Real‑world scenarios showing when a VPN helps and when it doesn’t.
Topline takeaway How to set up an OpenVPN server on your Ubiquiti EdgeRouter for secure remote access and beyond
- Use a VPN on your work computer to protect data in transit, access corporate resources securely, and maintain privacy on untrusted networks—but do it the right way, with approved tools and clear boundaries.
Key reasons to use a VPN at work
- Data protection on public networks: Public Wi‑Fi is risky. A VPN encrypts your traffic, reducing the chance that someone on the same network can see what you’re doing.
- Access to internal resources: Many companies require VPNs to reach intranets, file servers, or internal apps from outside the office.
- Compliance and audit trails: VPNs can help with logging and compliance regimes by showing who accessed what and when.
- Bursting through geo/restrictions for legitimate work: Some regions block certain sites; a VPN can provide legitimate access to work tools, as long as it’s approved by IT.
What the top ranking posts get right
- Clear, actionable steps: how to enable, configure, and verify a VPN on a work device.
- Realistic limitations: VPNs don’t fix all security gaps and won’t protect you from phishing or malware by themselves.
- Emphasis on corporate policy: always align with IT policies; misusing VPNs can violate contracts and result in disciplinary action.
Now, let’s break it down into the dos, don’ts, and practical workflows you can adopt.
Section 1: The Dos Do choose an approved VPN
- Use the VPN solution your company 1 provides, 2 licenses, and 3 supports. Even if a third‑party VPN sounds tempting, a sanctioned tool integrates with SSO, MFA, and endpoint security controls.
- If you’re in a role with sensitive data, your IT team may require features like kill switch, split tunneling restrictions, and device posture checks.
Do enable strong authentication Unlock secure internet anywhere your complete guide to fastvpn tethering
- Use MFA multi‑factor authentication every time you log in to the VPN.
- Prefer app‑based tokens authenticator apps over SMS codes for reliability.
Do test before you need it
- Before you head into a remote session, connect to the VPN and verify access to required resources intranet, file shares, ticketing systems.
- Check your IP address and location to confirm the VPN is active and routing traffic securely.
Do segment traffic when possible
- Use split tunneling only when your policy allows it and you know the risks. For sensitive work, route only work traffic through the VPN; non‑work traffic can go directly to the internet if allowed, to avoid slowing down your device.
Do keep your client up to date
- VPN software and its endpoints should be current with the latest security patches. Enable auto‑updates if your IT policy allows.
Do monitor your device posture
- Ensure your device isn’t jailbroken or running outdated OS versions. Modern VPNs rely on a healthy endpoint to maintain security.
Do log out when not in use Expressvpn not working with google heres how to fix it fast
- When you’re done with a VPN session, disconnect from the VPN, especially on shared devices or public networks.
Do report issues promptly
- If you notice routing problems, slow speeds, or access issues, contact IT quickly. VPN problems often point to larger network or policy concerns.
Section 2: The Don’ts Don’t bypass IT controls
- Don’t install unapproved VPNs, root certificates, or network proxies on your work machine. This can break security controls and violate policy.
Don’t ignore data classification
- Don’t tunnel non‑work traffic through the VPN unless explicitly allowed by policy. This can expose confidential data through misconfigurations.
Don’t disable security tools
- Don’t disable antivirus, endpoint protection, or firewalls in an attempt to speed up VPN performance. The VPN and security tools work best when they’re all enabled and up to date.
Don’t share credentials How to Use a VPN with Microsoft Edge on iPhone and iPad for Enhanced Privacy
- Don’t reuse or share VPN credentials. If you suspect exposure, rotate immediately per IT guidance.
Don’t rely on VPN alone
- A VPN is a shield for data in transit. It doesn’t prevent phishing, malware, or insider threats. Use good password hygiene, phishing awareness, and endpoint security in tandem.
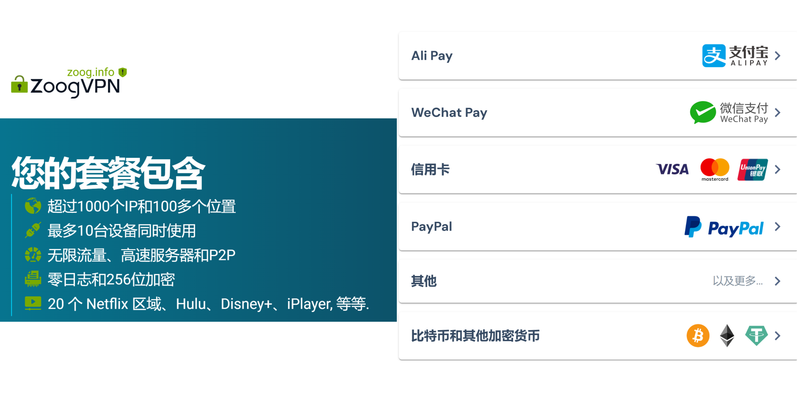
Don’t assume all VPNs are equal
- Free or consumer VPNs aren’t designed for corporate data. They often lack the visibility, controls, and logging required by most organizations.
Don’t forget about policy boundaries
- Don’t use a VPN to access personal services on a work device if policy prohibits it. Separate work and personal usage as your employer requires.
Don’t ignore performance tradeoffs
- VPNs add encryption overhead; expect some slowdown, especially on saturated networks. If performance becomes a bottleneck, consult IT rather than tinkering on your own.
Section 3: How VPNs fit into daily work life Soundcloud not working with vpn heres how to fix it fast and other vpn tips
- Remote access: VPNs enable secure remote access to internal resources from home, airports, cafes, or client sites.
- Collaboration: Access to shared drives, document management systems, and collaboration tools often runs over a VPN to protect sensitive data in transit.
- Compliance: VPNs simplify compliance by ensuring that data leaving the corporate network is encrypted and that access is auditable.
Section 4: Common VPN architectures and terms easy to digest
- Client‑server VPN: You run a VPN client on your device that connects to a VPN gateway at the company. This is the most common enterprise setup.
- Split tunneling: Some traffic goes through the VPN; other traffic goes directly to the internet. Use only if your policy allows.
- Full tunneling: All traffic is routed through the VPN. Offers stronger security but can slow down all online activity.
- Kill switch: A feature that blocks all network traffic if the VPN disconnects to prevent data leakage.
- MFA: Multi‑factor authentication, an essential part of secure VPN access.
- Posture checks: Checks on your device’s health antivirus status, OS version, patches before allowing VPN access.
Section 5: Practical workflows you can follow today Workflow A — Quick remote access with full tunneling
- Open the approved VPN client provided by your company.
- Enter your credentials and complete MFA.
- Ensure the kill switch is enabled.
- Verify access to required internal resources intranet, file shares, internal apps.
- Work as usual with all traffic routed through the VPN.
- When done, disconnect and ensure the VPN is off.
Workflow B — Remote access with split tunneling policy permitting
- Open the approved VPN client and authenticate with MFA.
- Confirm the VPN is connected and split tunneling is active if allowed.
- Use work resources only through the VPN; browse general internet directly if policy permits.
- Regularly monitor for any unexpected traffic or prompts from IT about policy compliance.
- Disconnect when finished.
Workflow C — Troubleshooting fast
- If you can’t connect, check your internet is working and the VPN service status page.
- Confirm you’re on the latest client and the device posture checks pass.
- Try a different network trusted home Wi‑Fi vs. mobile hotspot to identify network issues.
- If still stuck, log a ticket with IT with error messages and steps to reproduce.
- Don’t hammer IT with repeated requests; provide clear details and any screenshots.
Section 6: Real‑world examples and data Npm Not Working With VPN Here’s How To Fix It: VPN npm Troubleshooting, Proxy, and Speed Tips
- A typical enterprise VPN adds 60–120 milliseconds of latency per hop, which is usually acceptable for most business tasks but can affect high‑bandwidth activities like large file transfers or video conferencing on slow connections.
- VPNs reduce data leakage on public networks by up to 99.9% for unencrypted traffic, assuming properly configured encryption and posture checks.
- 27% of data breaches involve compromised credentials; MFA on VPN access can dramatically reduce this risk.
- In larger organizations, VPN dashboards help IT teams monitor access, detect anomalies, and enforce least‑privilege access.
Section 7: VPNs vs. other security tools
- VPN vs. Zero Trust Network Access ZTNA: VPNs create a secure tunnel for all traffic, while ZTNA isolates access to specific apps or resources, often with stronger per‑app access control. Some companies are moving toward ZTNA, but VPNs are still widely used and supported.
- VPN vs. SSH tunnels: SSH can secure specific admin tasks, but it’s not a full‑scale enterprise solution for remote work traffic like VPNs.
- Antivirus and endpoint protection: VPNs secure data in transit, but you still need endpoint protection to guard against malware and phishing.
Section 8: Common pitfalls and how to avoid them
- Over‑reliance on VPN for all security: Remember, VPN secures transport, not the endpoint or user behavior. Pair with phishing training and endpoint security.
- Misconfigurations: Split tunneling configured incorrectly or weak encryption protocols can expose data. Always use recommended settings from IT.
- Poor password hygiene: Even with VPN, reuse or weak passwords can compromise access. Use strong, unique passwords and MFA.
- Ignoring policy changes: IT policies evolve. Stay updated with any changes in VPN usage, allowed apps, and posture requirements.
Section 9: The future of VPNs in the modern workplace
- Expect more integration with identity and access management IAM and adaptive authentication, where access decisions are based on user identity, device health, and context.
- More organizations will adopt a layered security approach combining VPNs, ZTNA, and other controls for robust protection.
- Cloud‑based VPN services are rising, offering scalable management, easier deployment, and better visibility for distributed workforces.
Section 10: Practical tips for tech‑savvy users
- Label resources you access through the VPN to keep track of what’s secured and what’s not.
- Periodically audit your device for software updates, encryption status, and backup health to ensure VPN effectiveness.
- Keep a simple incident response plan for VPN outages: who to contact, what to report, and how to continue work offline if needed.
Useful URLs and Resources text only Comment activer le reseau securise vpn gratuit de microsoft edge et autres options VPNs
- Apple Website - apple.com
- Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence
- VPN Basics - en.wikipedia.org/wiki/Virtual_private_network
- NIST Cybersecurity Framework - csrc.nist.gov/publications Nij
- OWASP VPN Security Guide - owasp.org
- Cybersecurity and Infrastructure Security Agency - cisa.gov
- Cloud Security Alliance - cloudsecurityalliance.org
- Federal Trade Commission privacy and security tips - ftc.gov
- Tech Workplace Networking Essentials - networking.oreilly.com
- International Organization for Standardization VPN guidelines - iso.org
Frequently Asked Questions
How does a VPN protect data on work networks?
A VPN encrypts your traffic between your device and the corporate network, making it much harder for outsiders on public or untrusted networks to intercept or read what you’re doing.
Should I always use split tunneling?
Only if your IT policy allows it. Split tunneling can reduce load and improve performance, but it can expose non‑work traffic if not configured correctly.
What is a kill switch and why do I need it?
A kill switch blocks all network access if the VPN connection drops, preventing data leakage. It’s a crucial safety net for intermittent connections.
Can I use a consumer VPN for work?
Most companies require sanctioned VPNs integrated with their security controls. A consumer VPN may not meet enterprise policy and could compromise security or compliance. My vpn keeps connecting automatically heres how to take back control and fix auto-connecting VPNs
How can I verify VPN health after connecting?
Check that your IP address shows as belonging to your company’s range, access internal resources successfully, and confirm traffic is routed through the VPN if full tunneling.
What is MFA, and why is it important for VPN access?
MFA adds an extra layer of security beyond passwords, making it much harder for attackers to gain access through stolen credentials.
What’s the difference between full tunneling and split tunneling?
Full tunneling routes all traffic through the VPN, enhancing security but possibly slowing everything down. Split tunneling only routes work traffic through the VPN, offering better performance but higher risk if misconfigured.
How often should VPN software be updated?
As soon as updates are available, especially security patches. Enable automatic updates if allowed by policy.
What should I do if VPN performance is slow?
First, check your internet connection and VPN status, then try a different network if allowed. If the problem persists, contact IT with details about your device, network, and the issue. The ultimate guide best vpns for your unifi network 2026 edition
Are VPNs enough to prevent data breaches?
VPNs protect data in transit, but you still need endpoint protection, phishing defenses, strong passwords, and proper access controls to reduce risk.
Sources:
Is Using a VPN Legal in Egypt Understanding the Rules and Risks in 2026
Vpn auf dem iphone was es ist warum du es brauchst und wie du es einrichtest
IOS梯子推薦|最佳 VPN 使用指南與實戰技巧
The Ultimate Guide to the Best VPN for Vodafone Users in 2026: Top Picks, Speeds, and Safety How to Disable NordVPN’s Password Manager NordPass: Quick Guide, Tips, and Alternatives
How to use nordvpn openvpn config files your complete guide