How to set up an OpenVPN server on your Ubiquiti EdgeRouter for secure remote access and beyond
How to set up an OpenVPN server on your Ubiquiti EdgeRouter for secure remote access? Here’s a quick fact: OpenVPN on EdgeRouter gives you granular control, strong encryption, and seamless remote access to your home or small office network. In this guide, I’ll walk you through everything from prerequisites to validating the connection, with practical tips and a few pro tricks along the way. Think of this as a friendly, step-by-step setup you can follow end-to-end.
- Quick start overview
- Prerequisites and planning
- Installing and configuring OpenVPN on EdgeRouter
- Client certificate setup and deployment
- Firewall and NAT rules
- Testing the VPN connection
- Troubleshooting tips
- Security best practices
- Useful resources and templates
Practical quick links and resources text only
- EdgeRouter official docs - https://www.ubnt.com
- OpenVPN Project - https://openvpn.net
- Community VPN guides - en.wikipedia.org/wiki/Virtual_private_network
- UDP vs TCP overview - https://www.cloudflare.com/learning/ddos/glossary/udp-vs-tcp
- IPsec vs OpenVPN comparison - https://www.howtogeek.com/356856/openvpn-vs-ipsec-which-one-is-better/
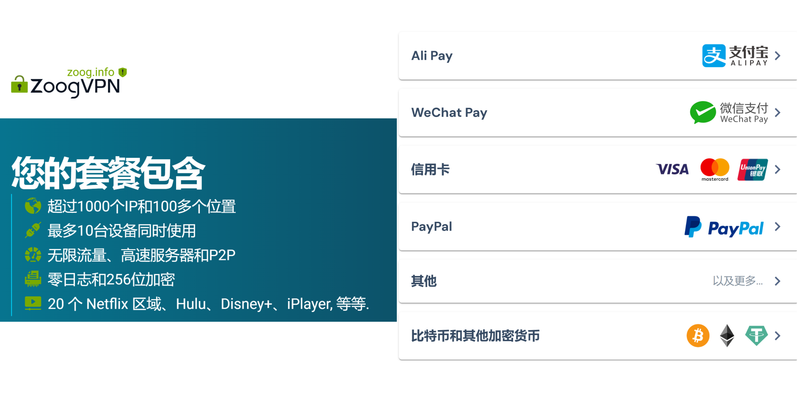
Note: If you’re looking for a quick way to secure your browsing and remote access with a trusted VPN, many readers also consider a commercial option. For a straightforward, user-friendly VPN with strong privacy features, you might want to check out NordVPN. Here’s a quick link to learn more: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441 Unlock secure internet anywhere your complete guide to fastvpn tethering
What you’ll achieve with this setup
- A secure, encrypted tunnel between remote devices and your local network
- Access to internal resources file shares, media servers, printers as if you were on-site
- Centralized control of VPN users and certificates
- Compatibility with multiple operating systems Windows, macOS, Linux, iOS, Android
Prerequisites and planning Before you touch the EdgeRouter, gather a few things:
- EdgeRouter model with a supported firmware version EdgeOS
- A static WAN IP or a reliable dynamic DNS service
- Administrative access to the EdgeRouter SSH or Web UI
- A dedicated certificate authority CA and server/client certificates, or be prepared to create them within the EdgeRouter
- A basic understanding of your LAN IP range to avoid conflicts
- A plan for firewall rules to limit exposure e.g., only VPN ports, not all ports
Step-by-step guide to set up OpenVPN on EdgeRouter
- Prepare your EdgeRouter
- Update EdgeRouter to the latest stable EdgeOS version for security and compatibility.
- Back up your current configuration so you can revert if needed.
- Confirm your WAN interface likely eth0 and your LAN subnet e.g., 192.168.1.0/24.
- Generate server and client certificates
- OpenVPN relies on certificates for trust. You can either use a built-in certificate authority on EdgeRouter or run EasyRSA on a separate machine and transfer the generated files to EdgeRouter.
- If you’re new to certificate management, using EasyRSA on a secure PC is a good starting point:
- Build a CA
- Generate a server certificate and key
- Generate client certificates for each remote device
- Generate a ta.key or use TLS-auth for extra security
- Install and configure OpenVPN on EdgeRouter
Note: The exact package installation can vary by firmware and model. If your EdgeRouter firmware doesn’t ship with OpenVPN packages, you can enable OpenVPN via built-in VPN features or install via SSH using available packages. Here’s the general approach:
- SSH into your EdgeRouter or use the GUI if your version supports it.
- Create a dedicated VPN directory for keys and config:
- mkdir -p /config/auth/openvpn
- cp /path/to/ca.crt /config/auth/openvpn/
- cp /path/to/server.crt /config/auth/openvpn/
- cp /path/to/server.key /config/auth/openvpn/
- cp /path/to/ta.key /config/auth/openvpn/ if using TLS-Auth
- cp /path/to/client.ovpn /config/openvpn/ example client file if using easy config
- port 1194
- proto udp
- dev tun
- ca ca.crt
- cert server.crt
- key server.key
- dh dh.pem if you generated a DH file
- server 10.8.0.0 255.255.255.0
- ifconfig-pool-persist ipp.txt
- push "redirect-gateway def1"
- push "dhcp-option DNS 1.1.1.1"
- push "dhcp-option DNS 8.8.8.8"
- keepalive 10 120
- tls-auth ta.key 0
- cipher AES-256-CBC
- user nobody
- group nogroup
- persist-key
- persist-tun
- status openvpn-status.log
- verb 3
- Configure firewall rules and NAT
- Allow UDP port 1194 or your chosen port inbound on the WAN interface:
- In EdgeOS, go to Firewall/NAT rules:
- Create a new firewall rule set for WAN_in
- Add a rule to accept UDP 1194 traffic to the OpenVPN server
- Leave other ports closed unless you intend to expose more services
- In EdgeOS, go to Firewall/NAT rules:
- Allow UDP port 1194 or your chosen port inbound on the WAN interface:
- Source NAT masquerade for the VPN network, typically 10.8.0.0/24, to the WAN interface
- Set up client profiles
- Each client will need an .ovpn profile that includes:
- client, dev tun, proto udp, remote your-wan-ip 1194
- resolv-retry infinite
- nobind
- persist-key
- persist-tun
- remote-cert-tls server
- ca ca.crt
- cert client.crt
- key client.key
- tls-auth ta.key 1
- cipher AES-256-CBC
- verb 3
- Each client will need an .ovpn profile that includes:
- Use password-protected zip files for transport
- Prefer S/MIME or a secure file sharing method
- For mobile devices, export .ovpn and import into OpenVPN Connect or the native OpenVPN app
- Enable and start the VPN service
- Start the OpenVPN service and enable it to start on boot:
- systemctl start openvpn@server
- systemctl enable openvpn@server
- Start the OpenVPN service and enable it to start on boot:
- systemctl status openvpn@server
- tail -f /var/log/openvpn.log or the corresponding log file
- Test locally and remotely
- Test locally inside your LAN first:
- Use a client device laptop or phone connected to the LAN
- Connect via OpenVPN to the EdgeRouter
- Confirm that the VPN interface comes up tun0 or similar and you can access internal devices
- Test locally inside your LAN first:
- From a different network cell data or public Wi-Fi, connect with the client profile
- Check that you can reach internal resources, test RDP/SSH/SMB as needed
Common issues and troubleshooting
- Connection refuses or times out
- Check that the OpenVPN service is actually running
- Validate firewall rules on the WAN_in and ensure UDP 1194 is allowed
- Confirm the server config paths and certificate locations
- Certificate or TLS handshake failures
- Ensure the ca.crt, server.crt, server.key, and ta.key are correctly referenced
- Confirm that the client is using matching client certificates
- IP address conflicts or routing problems
- Verify VPN subnet doesn’t overlap with LAN
- Check NAT rules and ensure VPN clients can reach LAN resources
- DNS leaks or slow name resolution
- Push a reliable DNS e.g., 1.1.1.1 and 8.8.8.8 to clients
- Test for DNS leaks and adjust client config if needed
Security best practices Expressvpn not working with google heres how to fix it fast
- Use TLS-auth tls-auth or TLS-crypt to protect the TLS handshake
- Prefer modern ciphers AES-256-CBC or AES-256-GCM if supported
- Use a unique, short-lived certificate for each client
- Regularly rotate certificates and keys
- Keep EdgeRouter firmware up to date and monitor for security advisories
- Limit VPN access to specific internal resources with firewall rules
- Consider multi-factor authentication for VPN access if your EdgeRouter supports it or layer with an identity provider
Advanced tips for power users
- Split tunneling: route only specific subnets through VPN to reduce bandwidth on the EdgeRouter
- Use DNS filtering on VPN clients to block malware domains while connected
- Create per-client firewall rules for additional security and auditability
- Enable comprehensive logging for VPN activity to monitor anomalous access
- Set up automated certificate renewal reminders to avoid expired credentials
Performance considerations
- VPN throughput depends on CPU; EdgeRouter models with stronger CPUs will handle more concurrent connections smoothly
- UDP generally offers better performance than TCP for VPN tunnels
- Wire through dedicated VPN hardware or offload tasks if your EdgeRouter supports it
- Monitor CPU and memory usage during peak hours to avoid bottlenecks
Best practices for maintaining a healthy VPN setup
- Regularly update all certificates and keys
- Keep an inventory of all client profiles and their expiry dates
- Periodically audit firewall rules to close any unused openings
- Back up OpenVPN configuration and keys securely
- Document your network topology and VPN access structure for future admins
Common use cases you’ll likely encounter
- Remote workers needing secure access to internal file shares
- Techies wanting to manage devices remotely without exposing ports to the internet
- Families wanting secure access to home media servers while traveling
- Small offices needing a cost-effective VPN solution without additional hardware
From setup to daily use: a quick reference checklist How to Use a VPN with Microsoft Edge on iPhone and iPad for Enhanced Privacy
- Verify WAN and LAN settings on EdgeRouter
- Generate server and client certificates
- Install and configure OpenVPN on EdgeRouter
- Create firewall and NAT rules to allow VPN traffic
- Prepare client profiles for all users
- Start the VPN service and perform thorough testing
- Harden security with TLS-auth, strong ciphers, and regular updates
Table: Key settings snapshot
- VPN protocol: UDP
- Default port: 1194
- VPN subnet: 10.8.0.0/24
- Encryption: AES-256-CBC
- TLS-auth: enabled
- Client count: 1..n scalable
- DNS for clients: 1.1.1.1, 8.8.8.8
- NAT: enabled for VPN subnet
User stories: real-world scenarios
- Remote access to a home lab: You’re on vacation but need to pull a file from your NAS. VPN gives you secure access as if you’re home.
- Small office access: Your team can securely reach internal tools like Jira, Git repositories, or internal wiki without exposing services to the internet.
- Family sharing: Allow a trusted family member to access media servers when they’re away, while keeping the rest of your network private.
Additional resources and templates
- OpenVPN quickstart guides and sample server.conf files
- EasyRSA or other certificate management templates
- EdgeRouter firewall rule templates for VPN setups
- VPN client profiles and distribution templates with secure packaging
Frequently Asked Questions
What is OpenVPN and why should I use it on EdgeRouter?
OpenVPN is a versatile, open-source VPN that creates secure tunnels over the internet. Running it on EdgeRouter gives you centralized control, strong encryption, and reliable remote access to your home or small office network. Soundcloud not working with vpn heres how to fix it fast and other vpn tips
Do I need a static IP for my EdgeRouter OpenVPN setup?
A static IP or a dynamic DNS service is recommended. It ensures clients can reliably connect to your VPN server. If your public IP changes, a dynamic DNS service keeps a hostname pointing to your current IP.
Can I use a different VPN protocol on EdgeRouter?
Yes, but OpenVPN is widely supported and straightforward to configure on EdgeRouter. Some users also deploy IPsec or WireGuard if supported by their hardware and firmware.
How do I distribute client certificates securely?
Generate a separate client certificate for each user, transfer the .ovpn file and certificates over a secure channel, and consider password-protecting sensitive files.
How can I ensure DNS privacy for VPN users?
Push a trusted DNS server to clients like 1.1.1.1 or 8.8.8.8 and optionally enforce DNS over HTTPS in client configurations.
Is TLS-auth necessary?
TLS-auth provides an additional HMAC signature on the TLS handshake, helping mitigate certain types of attacks. It’s recommended for better security. Vpn not working with sky broadband heres the fix
How do I test the VPN connection?
From a remote network, install the OpenVPN client, import the profile, connect, and verify access to internal resources. Check the VPN interface status and routing.
How can I restrict VPN access to specific devices or subnets?
Configure firewall rules to control which internal subnets or devices are reachable via VPN. This limits exposure if a client is compromised.
Can I use mobile devices with this setup?
Yes. Export client profiles as .ovpn files and import them into OpenVPN apps for iOS or Android. Ensure mobile devices have appropriate security measures.
What are common reasons VPN clients fail to connect?
Certificate mismatches, incorrect server address, firewall blocking UDP port, or VPN service not running are the usual culprits. Double-check each component and review logs.
How often should I rotate certificates and keys?
Plan a monthly or quarterly rotation, plus immediate rotation if you suspect a key compromise. Keep backups and revoke old certificates properly. Best Free VPNs for Roblox PC in 2026 Play Safely Without Breaking the Bank
How do I back up my VPN configuration?
Back up your OpenVPN server config, server and client certificates, keys, and any custom firewall rules. Store backups securely offsite.
Conclusion This guide gives you a solid path to set up OpenVPN on your EdgeRouter for secure remote access. While every network is unique, following these steps and keeping security best practices in mind will help you establish a robust, maintainable VPN. If you want a quick way to explore VPN options beyond OpenVPN, consider checking out reputable VPN providers for additional layers of protection and convenience. Remember to handle certificates, keys, and firewall rules with care, and you’ll have a reliable remote access solution that you can rely on.
Sources:
Nordvpn 30 day money back guarantee 2026: Comprehensive Guide to Refunds, Plans, and Privacy
Axgate vpn client 설치 최신 가이드와 알아야 할 모든 것 2026년 업데이트: 빠르고 안전한 연결을 위한 실전 팁
The Ultimate Guide Best VPN For Bug Bounty Hunting: Ultimate VPN Tips, Safe Browsing, and Pro Techniques Use a VPN on Your Work Computer: The Dos, Don’ts, and Why It Matters
Vpn不能用?别慌!手把手教你解决所有连接难题,附送稳定VPN推荐!
The Best Free VPNs for Your Cell Phone in 2026 Stay Secure Without Spending a Dime